I used Ida Pro Free 5 to solve this. Once loaded I started to look around. I found that the "GetAsyncKeyState" leads to something interesting.
This is what we get when we go to the function which calls it:
Basically it's a huge jump tree, where it will jump based on the hit keystrokes:
At the bottom we find a function for each key:
Most of the look like this, they call a single function:
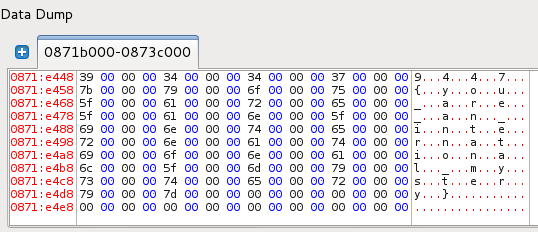
That function sets a bunch of variables, later these turn out to be represent states:
There are other functions for keystrokes, which look like the following:
It checks if a given variable is 0 or not, if yes, in this case it checks another one, and if that is also 0 t will call the very same initialization function I showed before, and if not 0, then it will set another variable to 1 and reset the currently interested one. This specific function is called when we press "0" as seen at the bottom.
What we can do from here is to try to navigate through the state graph back and forth, because we don't know where are we. First I started to go backwards, with finding out who change the state of the variable looked here. I was also started to give names to the functions and variables.
Then I moved forward with looking which is the next function looks into the set variable. This can be done with the menu "Jump to xref to operand":
Then select the next function (sub_10009B10 in this case):
At the end we can find that the keystroke sequence tracked is: l0ggingdoturdot5tr0ke5atflaredashondotcom
Which translates to: l0gging.ur.5tr0ke5@flare-on.com